March 30, 2026
5m 56s
Industrial control systems (ICS) have always been designed for reliability, safety, and availability. In 2026, those priorities remain, but the environment they operate in has fundamentally changed.
Long-standing industrial cybersecurity challenges are colliding with heightened pressures, including geopolitical tensions, new regulatory pressures, and massive growth in energy demand driven by AI and large-scale data centers.
For embedded developers, system designers, and product security teams, this shift is especially significant. The firmware and software running inside industrial devices are now both a primary attack surface and a critical line of defense. Unlike enterprise systems, embedded environments must balance security with strict constraints: limited compute, long deployment lifecycles, and real-time performance requirements.
The result is a clear inflection point. Industrial cybersecurity will need to place a greater focus on protection rather than detection. The next phase of industrial cybersecurity will be defined by resilience, built into software, devices, and software supply chains from the start.
Here are five embedded security shifts defining industrial cybersecurity in 2026.
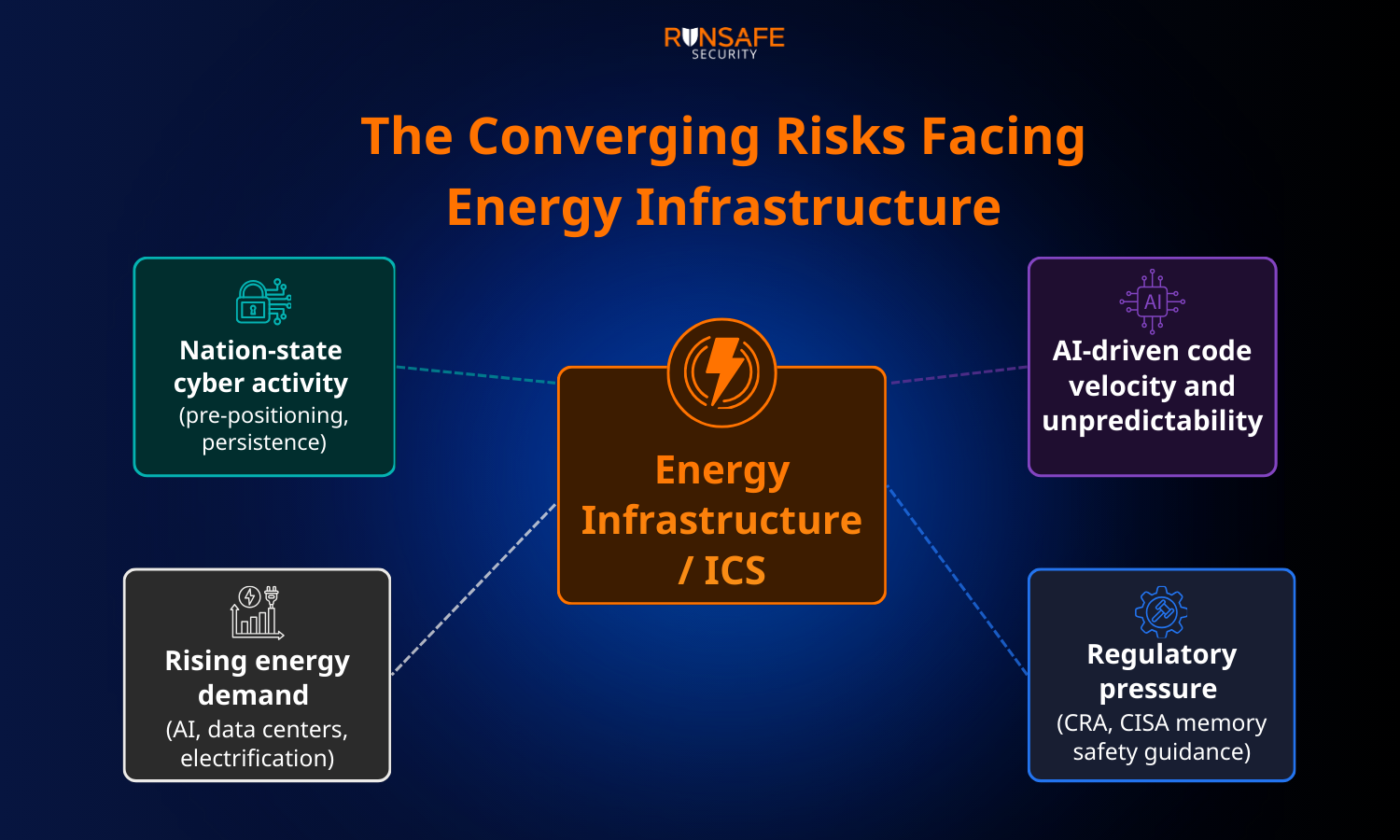
In 2026, attacks on industrial control systems are increasingly driven by geopolitical motivations rather than opportunistic cybercrime. Energy infrastructure, in particular, has become a strategic target not just for disruption, but for leverage.
We’ve already seen this play out in real-world conflict. Cyber operations targeting energy systems during the war in Ukraine demonstrated how cyberattacks have direct physical and economic consequences. Campaigns such as Volt Typhoon highlight how nation-state actors are pre-positioning in critical infrastructure, establishing persistent access in preparation for future conflict.
Additionally, news emerged at the beginning of December 2025 that the U.S. energy grid is exposed to China via a backdoor in inverters used within energy infrastructure. If operators don't start demanding and implementing cyber defense of these devices, those backdoors could be weaponized to trigger widespread blackouts and other disruptions at a time and place of China's choosing.
At the same time, rising energy demand driven by electrification, data centers, and AI workloads is increasing both the value and vulnerability of these systems.
For embedded systems, this elevates the importance of securing the devices themselves. Many energy systems rely on distributed embedded components—such as inverters, controllers, and field devices—that are difficult to patch and often deployed for decades. If compromised, these devices can serve as long-term footholds for adversaries.
AI is already part of everyday development in industrial environments. According to RunSafe Security’s “AI in Embedded Systems” report, more than 80% of embedded teams now use AI in development, and over 83% have deployed AI-generated code into production, including in industrial control systems and energy infrastructure.
Code that directly influences physical processes is being produced at a pace that would have been unthinkable just a few years ago.
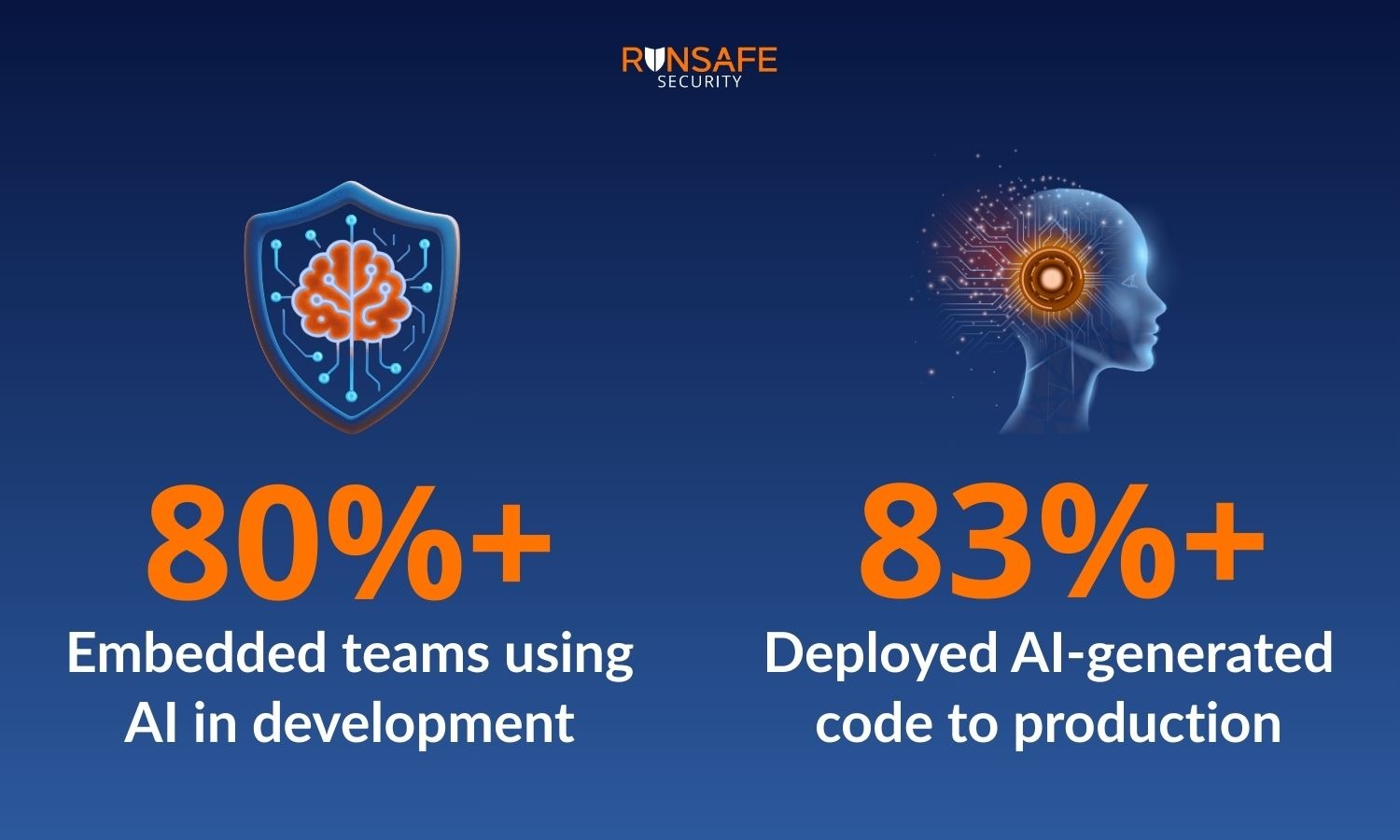
The speed cuts both ways. AI helps attackers move faster while introducing new challenges for defenders. AI-generated code is often less predictable than human-written software, weakening traditional threat models and expanding the software supply chain in unexpected ways. At the same time, AI gives engineering teams new ways to build, deploy, and secure systems more efficiently, even as resources remain constrained.
Recent joint guidance from global security agencies, including CISA, reflects this shift. The guidance recognizes that AI is no longer limited to enterprise tools or analytics platforms, but is increasingly shaping OT environments, including the firmware and controllers that run inside them.
As AI becomes more deeply embedded in ICS, resilience will matter more than perfection. Hardening software will allow organizations to adopt AI and manage the risks.
Despite growing risks, most industrial operators cannot simply replace legacy systems. ICS and SCADA assets are capitalized over decades, and full modernization cycles typically span 10 to 15 years or more. The economic and operational barriers to wholesale replacement remain too high.
That reality is forcing a shift in strategy. Rather than waiting for the next generation of secure devices, the industry is focusing on protecting systems already in place. This includes addressing well-understood vulnerability classes—particularly memory safety vulnerabilities—through software hardening and other proactive defenses that do not require rewriting code or replacing equipment.
Regulation is also a factor. The Cyber Resilience Act’s (CRA) requirements for software update mechanisms are one example that will push organizations toward more disciplined and often faster patch timelines. CISA’s designation of lack of memory safety as a Product Security Bad Practice, along with its call for manufacturers to publish memory safety roadmaps by January 1, 2026, signals that the industry can no longer afford to wait. The absence of update paths is no longer an excuse for delaying remediation.
In 2026, industrial cybersecurity is shifting toward deterministic runtime protection.
Rather than relying solely on network monitoring or anomaly detection, organizations are focusing on reducing exploitability directly within devices. This includes implementing protections that prevent entire classes of attacks from succeeding, even when vulnerabilities are present.
This approach is particularly important in embedded environments, where patching may be delayed or operationally risky.
By embedding protection into firmware and software, devices can defend themselves in real time without impacting performance or availability. This marks a shift from trying to detect every possible attack to ensuring that attacks cannot succeed in the first place.
2025 was the year of software supply chain attacks, and 2026 is shaping up to continue that trend. Going forward, transparency into industrial software supply chains will be a must. Regulations, like the CRA, are a major driver, but so is customer demand. Asset owners want clear insight into the components running in their environments, how vulnerabilities affect them, and how quickly issues can be addressed.
Build-time SBOMs give operators and manufacturers the visibility they need while strengthening software supply chain security across the ecosystem. Automatically generating SBOMs as part of the build process ensures accuracy, consistency, and traceability far beyond what static, manually assembled inventories can provide.
For embedded systems, this is especially valuable. Devices often include third-party libraries and components that persist in the field for years. Without clear visibility, vulnerabilities in these components can go undetected and unaddressed.
The long-standing security challenges facing ICS are not going away, but the industry’s response will make a difference in resilience.
AI-driven development and regulatory pressure are accelerating the need for a new security approach that starts at the device level. The organizations pulling ahead today are those that focus on reducing exploitability, protecting systems at runtime, and building transparency into their software supply chains.
For embedded systems, this means designing for resilience from the start and ensuring that devices can operate securely in an environment where threats are constant, and perfection is no longer a realistic assumption.